In case you missed it: Microsoft will stop using TLS 1.0/1.1 in Microsoft 365 by October 15, 2020. The date was pushed multiple times in the past and this deprecation was originally announced back in 2017. If you have not planned for this, you better read on!
What is the take on this?
Applications will stop connecting to Microsoft 365 to authenticate if the client does not have TLS 1.2 enabled. This can affect the browser or also the applications. Office client mostly relies on WinHTTP which is a Windows component. If the Operating system is capable to use TLS 1.2 you are fine. Windows 8 and newer support out of the box TLS1.2. Modern browsers also support TLS 1.2, so basically you can now lean back and relax.
I want more details!
Using Microsoft 365 is not only about having Office installed. There are many other services and interfaces which can be used to connect to it. So we need to check which clients are connecting to Microsoft 365 . For example, old Android Version 4.3 or earlier and Windows Phone 8 will fail. Some really old browsers also struggle, like Firefox version 5.0 and earlier versions, Internet Explorer on Window 7 or Safari 6.0.4/OS X10.8.4 and earlier versions. The Windows 7 OS can be configured to enable it for TLS 1.2. But there also other systems connecting to Exchange Online for example: Mail systems connecting to Exchange Online, other B2B Systems trying to connect to SharePoint uploading files, or even HR systems trying to reach out to graph or Azure AD. All these system finally now need to support TLS1.2!
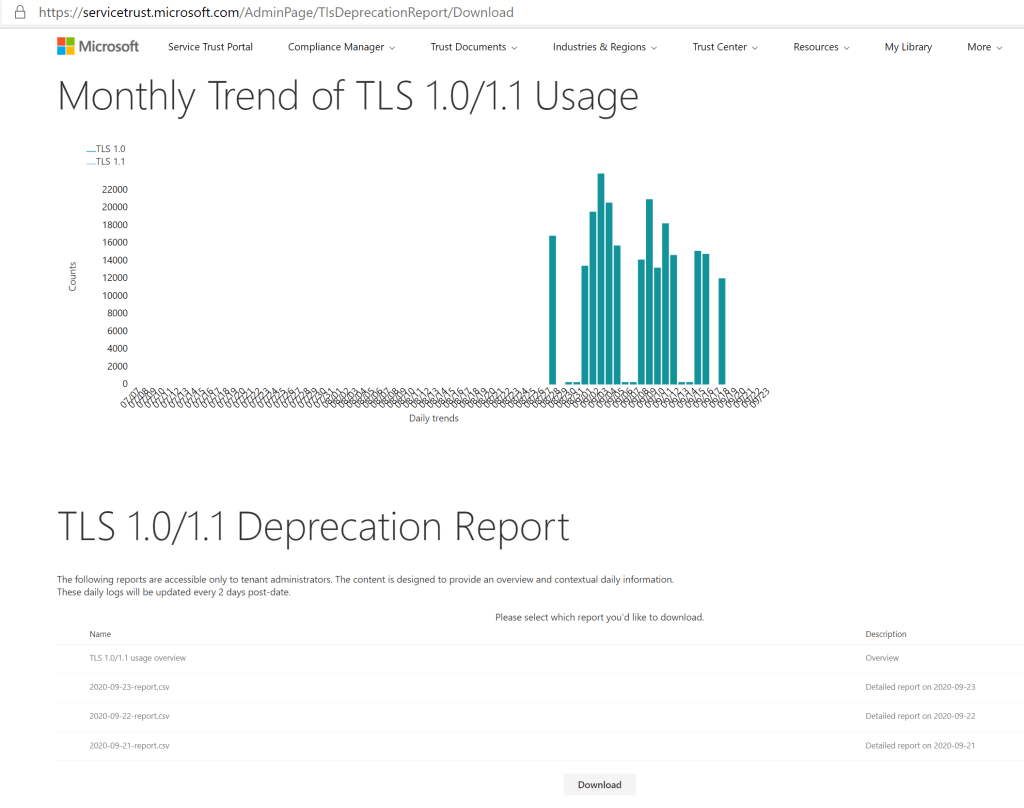
I need a report!
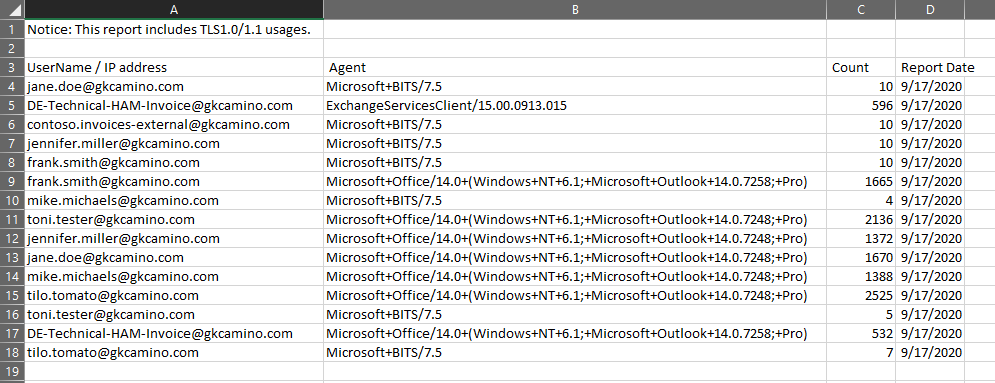
THe good news is Microsoft prepared something for you. The Service trust portal provides to Administrators a CSV report of devices still connecting with TLS 1.0/1.1.
Additional reports are available in the Office 365 Admin Center. Here you can get details on the SMTP clients and their authentication method to submit e-mails. The SMTP Auth (SMTP Authenticated Submission) protocol is primarily used by devices and applications that send automated messages on behalf of customers. For example, printers, other applications or even Business Partners which submit emails. To prevent sending unencrypted credentials, TLS is mandatory for SMTP Auth. So, when TLS 1.0 is disabled, no messages can be sent from devices or clients that do not support TLS 1.2. I have seen some older Multifunctional Printers and Scanner devices, which struggle with this twelve-year-old standard.
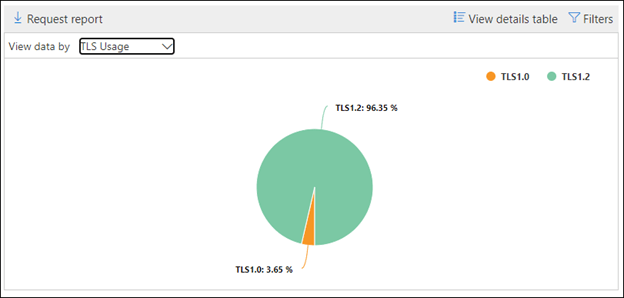
You can use SMTP Auth Client insight and Reports in the Security & Compliance Center to know which users are using this protocol, the volume of message sent, and the version of TLS used to connect to Office 365. Using this data, you can determine which clients and servers are still using TLS1.0 and TLS1.1 to connect to the various email protocol endpoints (like smtp.office365.com) in Exchange Online.

Click on the number of messages on the widget and SMTP Auth clients flyout appears. The flyout provides an aggregated view of the TLS usage and volumes for the last 7 days.
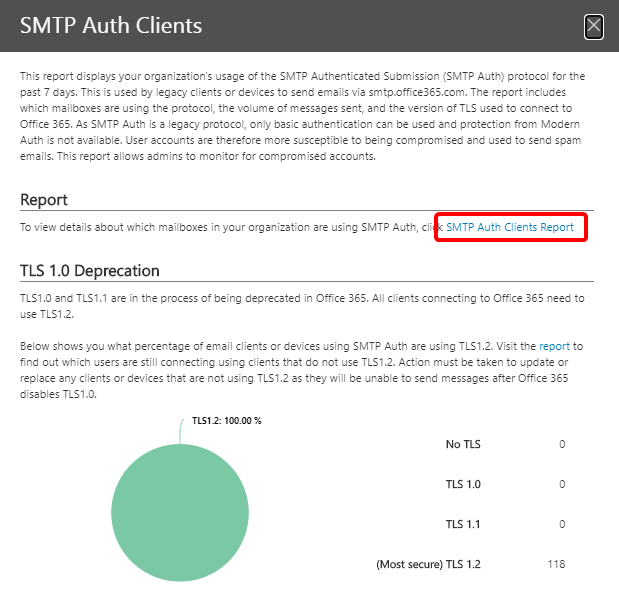
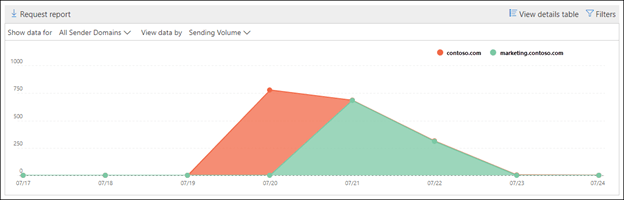
More details can be found when opening the SMTP Auth Clients Report. They give you an overview on the sent data volume and also the usage of the different versions of TLS.
What should I do?
Look at the above mentioned reports and check if you need to take action. The TLS deprecation report shows you a list of users who need to take action. In my example all these users will have an issue and cannot connect to Exchange anymore. It is a tedious work to reach out to all these users, and to find out why these users still have these old protocol enabled. In most of my cases is was just old devices not yet updated. If a user is using a Windows 10 with at least Office 2013 you will not have the issues. An Android 4.x phone is definitely old ands should be replaced due to other related security and update issues anyway.
By using the above reports, you can at least make the affected users visible and start an proactive communication and inform your support organizations
Soure:
https://docs.microsoft.com/en-us/microsoft-365/compliance/tls-1.0-and-1.1-deprecation-for-office-365
